The Ware for September 2023 is shown below.
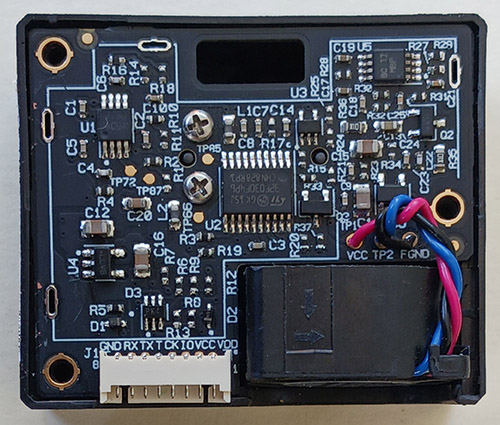
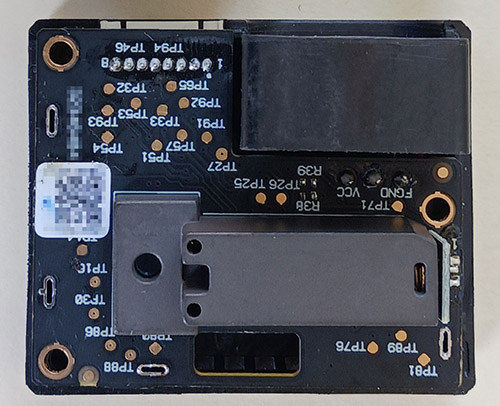
Thanks to FETguy for contributing this ware!
The Ware for August 2023 is a viewfinder from a JVC Super VHS Camcorder, model number GR-SXM915U. I’ll give the prize to Jin because of the correct identification of the SOIC as the BA7149F. Congrats, email me for your prize! The exact model number of the originating camera should be harder to pin down, because a similar viewfinder was probably used across several models for some years.
The viewfinder featured as this Ware has found a new life as part of a pretty neat project by the Ware’s contributor, Adrian: it displays a composite IR + visible light image, which is generated by glitching a live analog video stream from a visible light camera with an analog signal derived from a Pi Pico using an R2R DAC (i.e., the Pi Pico generates an analog signal almost directly off its digital GPIO via a resistor network — no DAC chip required). The Pico reads the H/V sync pulses encoded within the analog video stream, and overlays the digital readout of a 2D IR sensor by injecting well-timed pulses into the analog video signal (if I’m understanding the project correctly). More details and video at Adrian’s Mastodon post!
The Ware for August 2023 is shown below.
Thanks to adrian for sharing this ware! Adrian sent me several wonderful photos, and the whole thing is actually pretty neat to look at. However, for better or for worse the parts in the ware are so unique that most of them resolve to an answer with a simple search query – even those of the most humble looking 16-pin SOICs. Hopefully this partial view of the ware makes it at least a little bit of a challenge to guess.
The Ware for July 2023 is a “KUP 10” by aditec. Also, thanks to FETguy, we now have a schematic of the ware:
The spirit of Name that Ware is about demystifying electronics and encouraging people to learn by taking things apart. Drawing a schematic from an image of a circuit board is a great example of this, so FETguy gets the prize this month. Congrats, email me for your prize!
The “wäre” for July 2023 is shown below.
Thanks to zebonaut for submitting this ware. According to him, this was fished out of a dumpster in Germany, hence “wäre” (and yes, it’s a nonsense word, but I also think it’s cute). We had a little chuckle over the ware’s construction (or more precisely, the lack thereof). You could say, “they don’t build them like they used to” — could something like this pass certification in modern Germany? Well, it seemed to have at least passed the test of time, since it only recently found its way into a dumpster, and the rating label indicates a manufacturing date from the 14th week of 1996.
FETguy has contributed schematics for the ware, which he reverse engineered by hand:
A big thanks for contributing these! The spirit of Name that Ware is to inspire people to learn about electronics by taking things apart and observing their construction — and reverse engineering schematics is the asymptotic limit of that spirit!