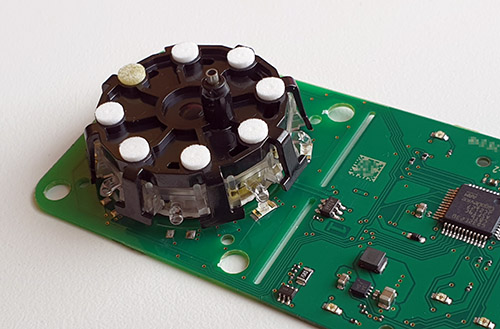
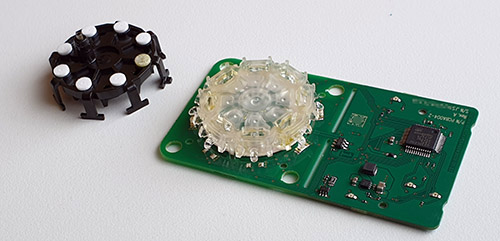
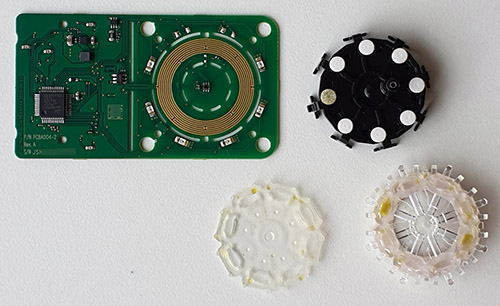
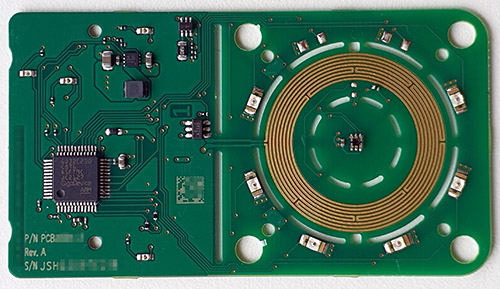
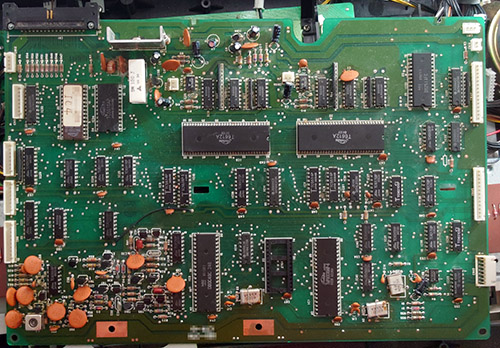
The Ware for December 2023 is shown below.
Thanks to Cedric Honnet for contributing this ware! Unfortunately this image does have an exact hit on Google images, as it is already in Cedric’s social media feed — but I think the ware itself is functionally interesting, yet simple enough to guess without having to rely on image searches.
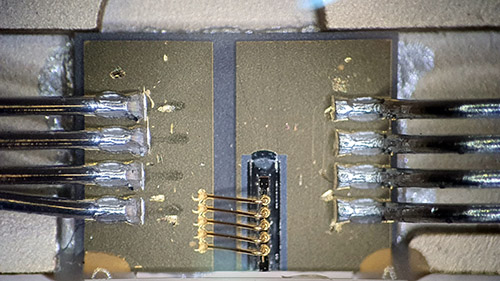
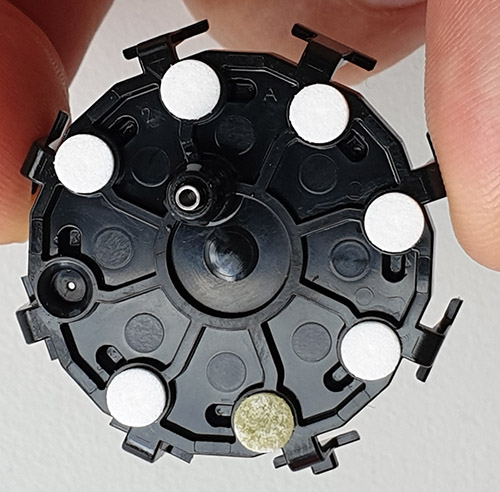
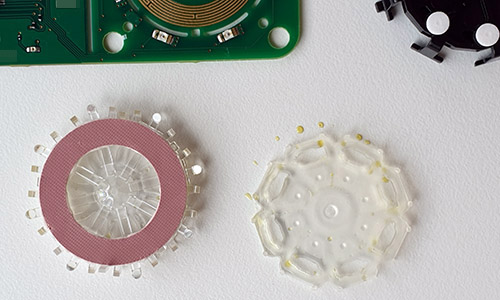
Thus answers will be judged in part based on their insight into the reasoning behind the construction of this ware — for example, what’s going on in the zoomed in view of the ware? What are some of the considerations in building a module of this nature?
Happy new year! Name that ware will be wrapping up its 18th year soon